Visibility and access controls (CORE ONLY)
GitLab allows administrators to enforce specific controls.
To access the visibility and access control options:
- Log in to GitLab as an admin.
- Go to Admin Area > Settings > General.
- Expand the Visibility and access controls section.
Default branch protection
This global option defines the branch protection that applies to every repository's default branch. Branch protection specifies which roles can push to branches and which roles can delete branches. In this case Default refers to a repository's default branch, which in most cases is master. branches. "Default" in this case refers to a repository's default branch, which in most cases would be "master".
This setting applies only to each repositories' default branch. To protect other branches, you must configure branch protection in repository. For details, see Protected Branches.
To change the default branch protection:
- Select the desired option.
- Click Save changes.
For more details, see Protected branches.
Default project creation protection
Project creation protection specifies which roles can create projects.
To change the default project creation protection:
- Select the desired option.
- Click Save changes.
For more details, see Default project-creation level.
Default project deletion protection (PREMIUM ONLY)
By default, a project can be deleted by anyone with the Owner role, either at the project or group level.
To ensure only admin users can delete projects:
- Check the Default project deletion protection checkbox.
- Click Save changes.
Project deletion adjourned period (PREMIUM ONLY)
Introduced in GitLab 12.6.
By default, project marked for deletion will be permanently removed after 7 days. This period may be changed.
To change this period:
- Select the desired option.
- Click Save changes.
Default project visibility
To set the default visibility levels for new projects:
- Select the desired default project visibility.
- Click Save changes.
For more details on project visibility, see Public access.
Default snippet visibility
To set the default visibility levels for new snippets:
- Select the desired default snippet visibility.
- Click Save changes.
For more details on snippet visibility, see Public access.
Default group visibility
To set the default visibility levels for new groups:
- Select the desired default group visibility.
- Click Save changes.
For more details on group visibility, see Public access.
Restricted visibility levels
To set the available visibility levels for new projects and snippets:
- Check the desired visibility levels.
- Click Save changes.
For more details on project visibility, see Public access.
Import sources
To specify from which hosting sites users can import their projects:
- Check the checkbox beside the name of each hosting site.
- Click Save changes.
Project export
To enable project export:
- Check the Project export enabled checkbox.
- Click Save changes.
For more details, see Exporting a project and its data.
Enabled Git access protocols
Introduced in GitLab 8.10.
With GitLab's access restrictions, you can select with which protocols users can communicate with GitLab.
Disabling an access protocol does not block access to the server itself via those ports. The ports used for the protocol, SSH or HTTP(S), will still be accessible. The GitLab restrictions apply at the application level.
To specify the enabled Git access protocols:
- Select the desired Git access protocols from the dropdown:
- Both SSH and HTTP(S)
- Only SSH
- Only HTTP(S)
- Click Save changes.
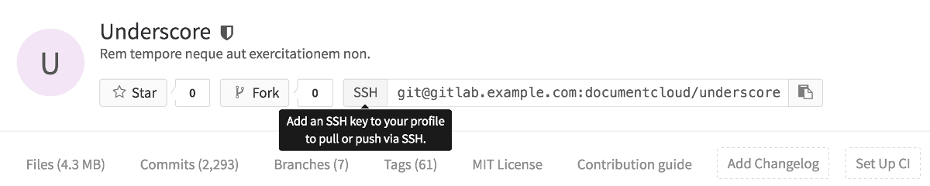
When both SSH and HTTP(S) are enabled, users can choose either protocol.
When only one protocol is enabled:
- The project page will only show the allowed protocol's URL, with no option to change it.
- A tooltip will be shown when you hover over the URL's protocol, if an action on the user's part is required, e.g. adding an SSH key, or setting a password.
On top of these UI restrictions, GitLab will deny all Git actions on the protocol not selected.
CAUTION: Important: Starting with GitLab 10.7, HTTP(S) protocol will be allowed for Git clone or fetch requests done by GitLab Runner from CI/CD jobs, even if Only SSH was selected.
Custom Git clone URL for HTTP(S)
Introduced in GitLab 12.4.
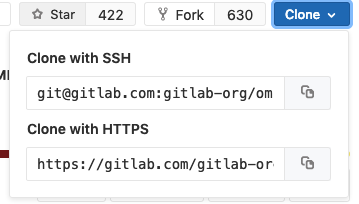
You can customize project Git clone URLs for HTTP(S). This will affect the clone panel:
For example, if:
- Your GitLab instance is at
https://example.com, then project clone URLs are likehttps://example.com/foo/bar.git. - You want clone URLs that look like
https://git.example.com/gitlab/foo/bar.gitinstead, you can set this setting tohttps://git.example.com/gitlab/.
To specify a custom Git clone URL for HTTP(S):
- Enter a root URL for Custom Git clone URL for HTTP(S).
- Click on Save changes.
NOTE: Note:
SSH clone URLs can be customized in gitlab.rb by setting gitlab_rails['gitlab_ssh_host'] and
other related settings.
RSA, DSA, ECDSA, ED25519 SSH keys
These options specify the permitted types and lengths for SSH keys.
To specify a restriction for each key type:
- Select the desired option from the dropdown.
- Click Save changes.
For more details, see SSH key restrictions.
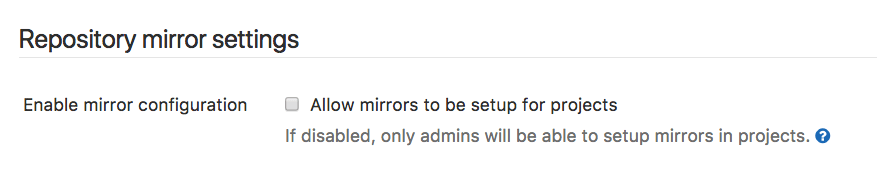
Allow mirrors to be set up for projects
Introduced in GitLab 10.3.
This option is enabled by default. By disabling it, both pull and push mirroring will no longer work in every repository and can only be re-enabled by an admin on a per-project basis.